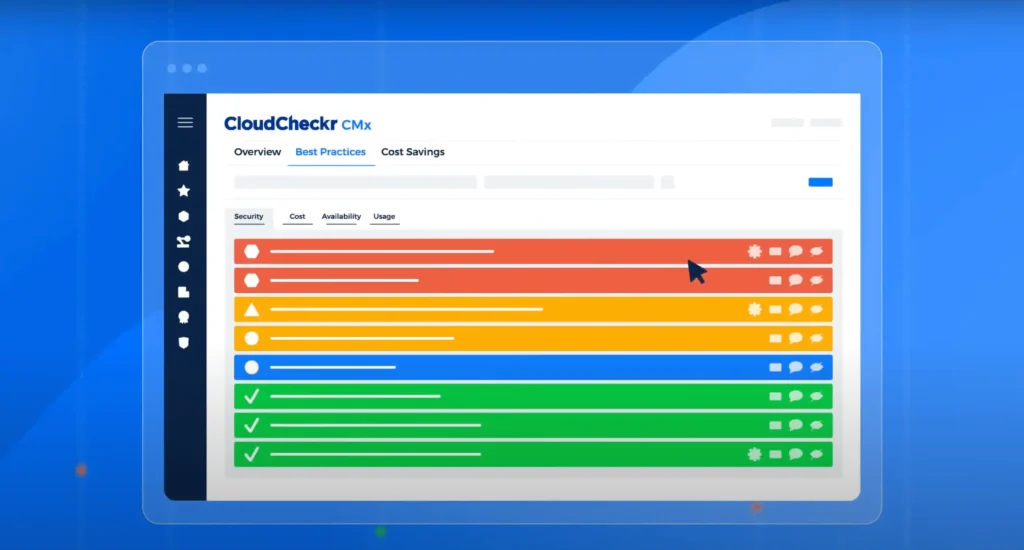
Optimize your cloud
A foundational solution for FinOps, CloudCheckr from Spot by NetApp is a robust cloud management platform designed to support large enterprise organizations and managed service providers (MSPs). CloudCheckr enables you to better manage and reduce cloud costs, optimize resources and gain operational efficiencies, improve governance, and strengthen security and compliance— all within a single platform.
CloudCheckr provides unique visibility and analytics together with hundreds of best practice checks and automation to deliver the most comprehensive solution for cloud management.

Understand & control cloud costs
Gain actionable visibility
Get deep visibility into current and historical cloud spend. Know what cloud services and resources are in use, by whom, and how they are driving costs and consumption to make informed decisions based on accurate data.
Optimize cloud costs
Continually optimize cloud spend – by 30% or more – by identifying opportunities to right-size and rebalance instances and acting on CloudCheckr’s purchase recommendations for commitment discounts.
Assess resource efficiency and remove waste
Track long-term resource consumption trends and identify opportunities to improve utilization and eliminate waste across your cloud estate. Quickly detect, investigate, and respond to cost overruns.
Accurately chargeback/showback costs
Manage costs and ensure accountability by precisely allocating cloud consumption to the right cost center, business unit, product line, project, team, or other entity.
Improve security and compliance
Reduce risk by automatically identifying infrastructure misconfigurations and vulnerabilities, many with self-healing automation.